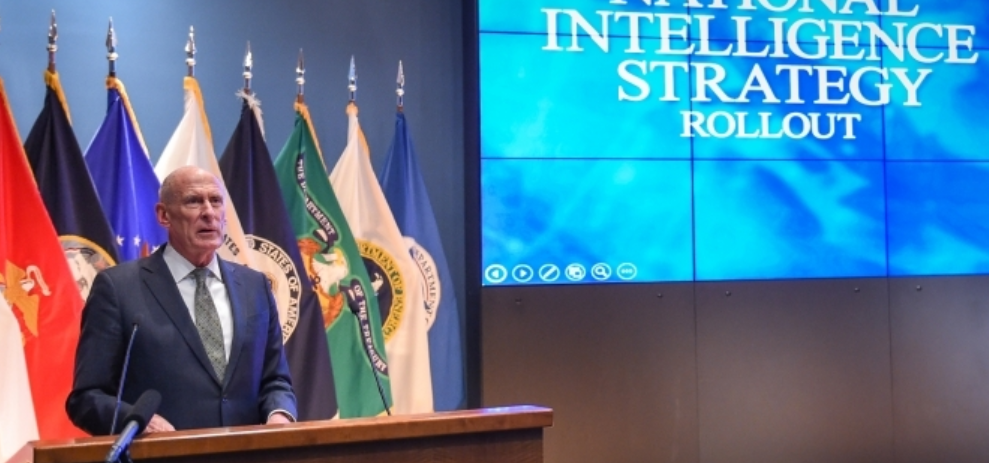
US Director of National Intelligence (DNI) Daniel R. Coats releases the 2019 National Intelligence Strategy (NIS), highlighting technological threats and how the Intelligence Community (IC) will tackle these.
“We have to become much more agile, more innovative, more creative.“
— Daniel R. Coats, Director of National Intelligence
“Our adversaries are increasingly leveraging rapid advances in technology to pose new and evolving threats — particularly in the realm of space, cyberspace, computing, and other emerging, disruptive technologies,” the NIS report released on Tuesday reads.
Read More: ‘Man-machine teaming’ is a ‘critical element’ in AI competition with China: Joint Chiefs Chairman
“Technological advances will enable a wider range of actors to acquire sophisticated capabilities that were previously available only to well-resourced states.”
Perceived technological threats require countermeasures, and the NIS report outlines how the IC will tackle these technological threats from its “adversaries.”
The NIS report puts heavy emphasis on innovation, partnerships, and transparency.
Technological Threats and Countermeasures
 Here are some of the perceived technological threats to US national security and their solutions for the next four years.
Here are some of the perceived technological threats to US national security and their solutions for the next four years.
Perceived Threat: Disruptive tech in the hands of adversaries is driving evolutionary change across multiple fronts
While the IC remains focused on confronting a number of conventional challenges to U.S. national security posed by its adversaries, advances in technology are driving evolutionary and revolutionary change across multiple fronts.
Countermeasures: Continuing and advancing cooperation with partners and allies
The IC will have to become more agile, innovative, and resilient to deal effectively with these threats and the ever more volatile world that shapes them. The increasingly complex, interconnected, and transnational nature of these threats also underscores the importance of continuing and advancing IC outreach and cooperation with international partners and allies.
Perceived Threat: Democratization of emerging tech allows data to be shared farther and faster
Advances in communications and the democratization of other technologies have also generated an ability to create and share vast and exponentially growing amounts of information farther and faster than ever before.
Emerging technologies, such as artificial intelligence, automation, and high performance computing are advancing computational capabilities that can be economically beneficial, however these advances also enable new and improved military and intelligence capabilities for adversaries of the US.
Read More: DoD needs ‘more of a startup mentality when looking at tech like AI’: Defense CIO
Some violent extremist groups will continue to take advantage of these sources and drivers of instability to hold territory, further insurgencies, plan external attacks, and inspire followers to launch attacks wherever they are around the world.
Countermeasures: To counter these threats in accordance with IC authorities, with appropriate levels of transparency to the public, and with adequate protection for civil liberties and privacy
All of these issues will continue to drive global change on an unprecedented scale and the IC must be able to warn of their strategic effects and adapt to meet the changing mission needs in this increasingly unstable environment.
There will likely be demand for greater intelligence support to domestic security, driven in part by concerns over the threat of terrorism, the threat posed by transnational illicit drug and human trafficking networks, and the threat to U.S. critical infrastructure.
Intelligence support to counter these threats must be conducted in accordance with IC authorities, with appropriate levels of transparency to the public, and with adequate protection for civil liberties and privacy.
Perceived Threat: Cyberattacks
Despite growing awareness of cyber threats and improving cyber defenses, nearly all information, communication networks, and systems will be at risk for years to come.
Adversaries are becoming more adept at using cyberspace capabilities to threaten our interests and advance their own strategic and economic objectives. Cyber threats will pose an increasing risk to public health, safety, and prosperity as information technologies are integrated into critical infrastructure, vital national networks, and consumer devices.
Countermeasures: To meet these evolving cyber threats as a part of a comprehensive cyber posture positioning the Nation for strategic and tactical response.
To meet this objective, the IC will:
- Increase its awareness and understanding of adversaries’ use of cyber operations—including leadership plans, intentions, capabilities, and operations—to inform decisions and enable action.
- Expand tailored production and appropriate dissemination and release of actionable cyber threat intelligence to support the defense of vital information networks and critical infrastructure.
- Expand its ability to enable diplomatic, information, military, economic, financial, intelligence, and law enforcement plans and operations to deter and counter malicious cyber actors and activities.
Perceived Threat: Foreign Intelligence Entities (FIEs)
Rapid technological advances are allowing a broad range of FIEs to field increasingly sophisticated capabilities and aggressively target the government, private sector partners, and academia.
Read More: Tech arms race with China blurs ‘physical, digital, biological lines’: WEF
FIEs are proactive and use creative approaches—including the use of cyber tools, malicious insiders, espionage, and supply chain exploitation — to advance their interests and gain advantage over the United States.
Countermeasures: Work with partners, develop better detection and deterrence capabilities
To meet this objective, the IC will:
- Drive integrated IC activities to anticipate and advance its understanding of evolving FIE threats and security vulnerabilities.
- Develop and implement new capabilities to detect, deter, and disrupt FIE activities and insider threats.
- Advance counterintelligence (CI) and security efforts to protect our people, technologies, information, infrastructure, and facilities from FIEs and insider threats.
- Strengthen the exchange of FIE threat and security vulnerability information among key partners and stakeholders to promote coordinated approaches to mitigation.
The National Intelligence Strategy
The Office of the Director of National Intelligence (ODNI) oversees the coordination and integration of the 17 federal organizations that make up the Intelligence Community.
Read More: US defense intelligence warns of AI-human hybrid soldiers from China
The NIS is one of the most important documents for the IC, as it aligns IC efforts to the National Security Strategy, sets priorities and objectives, and focuses resources on current and future operational, acquisition, and capability development decisions.
“This, the fourth iteration of the National Intelligence Strategy (NIS), is our guide for the next four years to better serve the needs of our customers, to help them make informed decisions on national security issues, and to ultimately keep our Nation safe,” DNI Coats wrote in the opening of the NIS report.
To guide the IC in facing these challenges, the NIS identifies and explains the IC’s objectives – both what the Community must accomplish (mission objectives) and what capabilities the Community must build in order to do so (enterprise objectives).
The seven mission objectives are 1) strategic intelligence; 2) anticipatory intelligence; 3) current operations intelligence; 4) cyber threat intelligence; 5) counterterrorism; 6) counterproliferation; and 7) counterintelligence and security.
The seven enterprise objectives are 1) integrated mission management; 2) integrated business management; 3) people; 4) innovation; 5) information sharing and safeguarding; 6) partnerships; and 7) privacy, civil liberties, and transparency.